Overview
TSTAR is a simulation control framework (services) and a collection of models and tools.
Integrates models, such as hardware and environment, with computer programs to create complex system representations. Computer programs are models or re-compiled tactical programs.
Verified TSC models include:
- Environment models: propagation, clutter, targets
- Radar hardware models: AN/SPY-1 and AN/SPQ-9B
- Specification models: C&D, WCS, FCS, VLS, CEP, CDLMS, AN/SPQ-9B air
- Weapon models: SM-2/6/3, ESSM 3+ DoF (all blocks); MK 45 Gun
Available separately with permission:
- Aegis re-hosted (re-compiled for change/debug) tactical programs
- AN/SPQ-9B tactical air tracker; CEC tactical model
- 6 DoF Weapons
Simulates multi-platform scenarios with complex threat/environment
Runtime display/control and post-run data analysis tools
Leverages TCE technology and development team SMEs
Benefits
Runs non-real time (usually faster), supports high-fidelity sensors/threats, accessible debug capability with reproducibility
Supports team sharing for development and test with many replications on low requirements hardware
Plug and play processing environment support
Analysis Support Tools Available:
- Automated Build
- Data Analysis and Visual Display (DAViD)
- Automation/Grid processing
- Automated Performance Assessment (APA)
Additional Details
- Common environment:
- AAW, BMD, surface, and interceptor debris models
- Electronic Attack models
- Non-standard propagation
- Sea, site-specific land, chaff, weather
- Monte Carlo controller
- Operator model
Hardware/ Software Requirements
- Windows 10 or Linux RHEL 8
- Dual/multi-monitor recommended
- Quad-core, 2GHz processor or better
- 16+GB RAM or better 100 GB HD or better
TSTAR Framework Design
- Service provider (configuration, data access, data recording, event/message routing, event scheduling, time of day access, more)
- Extensible configuration (virtual CPUs)
- Disperse processing (multi-node, multi-platform)
- Emulates dispersed processing
- Features for diagnostics
- Timing analysis
- Message send/receive statistics
- Message publish/subscribe data
- Event log
- User system controls
- GUI interface
- Integrates well with tactical computer programs
Allows for much greater scope of development and test on PC/workstation
TSTAR Sample Configuration
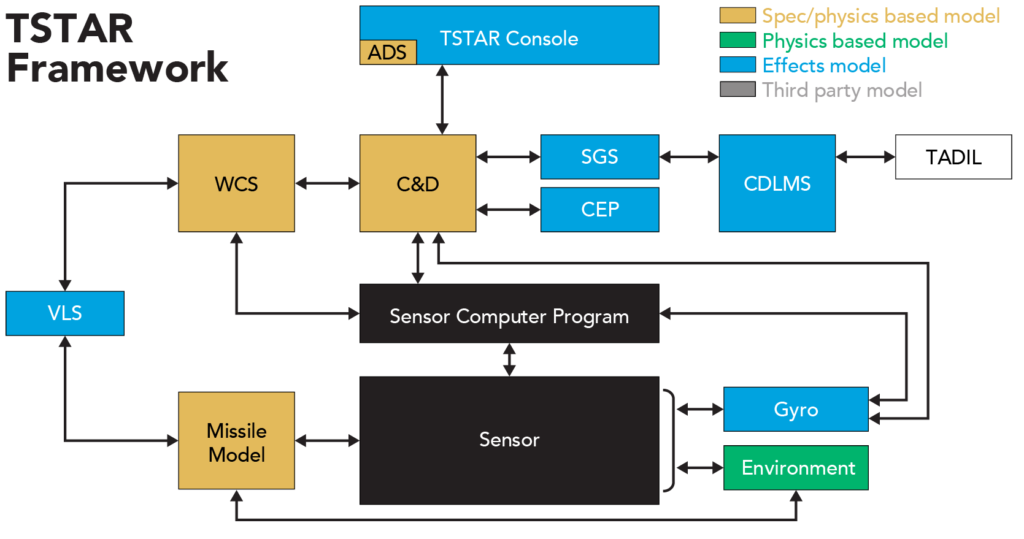
- Subset configurations available to suit customer needs
- Interfaces of all models are in accordance with tactical definitions; multiple baselines/versions are supported (i.e. Aegis BL 5, 7, 9o8, 9.2.0, 9.2.1, 9.2.2, 9.2.3)
- FMS available with permission
- Additional/substitute customer tactical components and/or representative models can be integrated into TSTAR
Experience the power of the virtual theater!
TSTAR is based on TCE technology
- TCE has been used by the SPY-1 community since 2001
- Predecessor (ADAM) used since 1993 for SPY-1 analysis
- TCE supports the Combat Systems Test Bed (CSTB), a PEO-IWS and MDA official high-fidelity representation of the Aegis Combat System
- TCE is accredited by PEO IWS1 and OTF for Baseline 9 Runs for the Record
Models
| Framework | Since 2001, developed by TSC |
| Environment Model | Since 2001, developed by TSC
|
| SPY-1 Hardware Model | Since 1993, developed by TSC – verified with at-sea data from numerous at-sea events |
| SPQ-9B Hardware Model | Since 2005, developed by TSC – used as part of LPD-17 PRA (official validated tool suite) |
| Missile Model | Since 2005, based on SPY SDM model – registered with APL’s SM2 6DoF accredited model for SM2 |